From novice to expert: Anna Barrett’s transformational apprenticeship experience
Reading Time: 3 minutes An apprenticeship is a great way of training for a career in IT. Typically, it’s 18 months of intense training and lots of study.
Unlocking your company’s IT potential: the power of a dedicated technical account manager
Reading Time: 3 minutes IT outsourcing is a powerful and effective way to access specialised skills, reduce costs, and increase the efficiency of your IT network.
MobileFlex: a game-changer in business mobile communication for today and beyond
Reading Time: 2 minutes Now CNC is part of the FluidOne Group of Companies, we have a lot of extra services to offer our customers, including mobile connectivity.
The recent cybercrime wave: why are NHS, Ticketmaster & Santander vulnerable?
Reading Time: 7 minutes June was a black month with some of the worst cyber hacks perpetrated in 2024 so far. Ticketmaster, the NHS and Santander were all in the national press, with news of them being hacked by cyber terrorists.
Empowering businesses with Litigation Hold and eDiscovery in Microsoft 365 Business Premium
Reading Time: 4 minutes In the fast-paced world of business, data plays a pivotal role in decision-making, collaboration, and overall success. However, with great data comes great responsibility, especially when it comes to legal matters.
How to use your smartphone in the art of disconnecting
Reading Time: 3 minutes Switching off from work can be hard. There’s an expectation to be “always on”, where your personal life and your business world never separate. Here’s how to get a minute or two to practice the art of stone stacking.
If there’s something strange in your IT network, who ya gonna call?
Reading Time: 3 minutes This time 40 years ago in June 1984, Ghostbusters was the number one film.
Our new service desk teams: how this will work for you.
Reading Time: 2 minutes Our service desk has undergone in recent months some changes. As part of CNC’s continuous improvement programme, we have revised how our helpdesk structure resolves your IT problems.
Stay safe and secure: cyber tips for when you’re on the move
Reading Time: 5 minutes So, you’ve been going through your checklist before you fly off on your business trip: encrypt or delete sensitive files? CHECK. Tamper seals over the hard drive access points? CHECK. Spare USB port locks? CHECK, privacy screen? CHECK. Was it always like this?
Using 7zip when Windows fails you
Reading Time: 3 minutes In this quick guide we’ll show you how to unzip and create ZIP files using 7zip.
Remembering passwords can be a real headache.
Reading Time: 3 minutes I can remember how much it cost to see Star Wars, my first car’s registration plate or who was number 1 in the charts, 30 years ago, but a password from yesterday?
Starlink success: A game-changer in internet access
Reading Time: 2 minutes A glowing review from a customer about a supplied product beats any marketing material. Starlink proves to be a major success for forward-facing surveyors. Here is how:
An evolution of cyber crime: The rise of cyber scam factories
Reading Time: 3 minutes There are many sides to cyber crime. However, there is another aspect of the horror of cyber crime that is the cyber scam factory.
Pen Testing – let me explain
Reading Time: 5 minutes In the IT industry, we have a penchant for acronyms. If we can condense the name of a service, product, or piece of equipment into just three letters, we’re as happy as a lark.
It couldn’t have happened to a nicer bunch of cybercriminals
Reading Time: 3 minutes The world’s largest criminal ransomware gang (Lockbit) have not only been infiltrated by the UK’s National Crime Agency (NCA) but they have had their data stolen.
Using Microsoft’s roadmap for your business
Reading Time: 2 minutes Running a business and keeping abreast of all the technological things that are sent your way can be pretty daunting. See what’s on the horizon with Microsoft Roadmap.
FluidOne goes the extra mile for FareShare in 5K charity event
Reading Time: 2 minutes FluidOne takes FareShare cause to heart, with a 5K run organised for this July, to help raise funds for this great charity.
365 Backups: your insurance policy against data loss and disasters
Reading Time: 5 minutes Joke for you: Why don’t clouds use Microsoft services? Because even in the sky, they can’t find a backup!
SonicWall SSLVPN – Enhanced (SMA)
Reading Time: 4 minutes A VPN allows you to access resources on your office network from wherever you are. SonicWall NetExtender is a piece of software that can be installed on your laptop or desktop that initiates the VPN connection.
Southern Water: faces reputational fallout with confirmed cyber hack
Reading Time: 3 minutes Southern Water now admits that as many as half a million customers’ personal information may have been stolen in the recent cyber attack.
What you need to know about the PSTN switch-off
Reading Time: 2 minutes Every technology has its day and now, it’s time to take the next step forward in the evolution of telecommunications.
All you need to know about an IT Risk Register
Reading Time: 2 minutes Over the next few months, we’ll be putting together a Risk Register for each of our customers and placing it on the Portal for you.
Business showdown: cloud service vs. on-premise solutions
Reading Time: 5 minutes In the late autumn of 1965, the Rolling Stones released ‘Get off my cloud’. It’s one of the band’s signature tunes, reaching the number-one spot in the UK, the US, Canada and Germany. They could have never imagined that the title of their song would have such relevance today.
Staying one step ahead: phishing, vishing, and smishing
Reading Time: 4 minutes Phishing, vishing, and smishing sound like the names of small villages on a beautiful coastline in some faraway paradise, but I can assure you these names stand for something completely onerous.
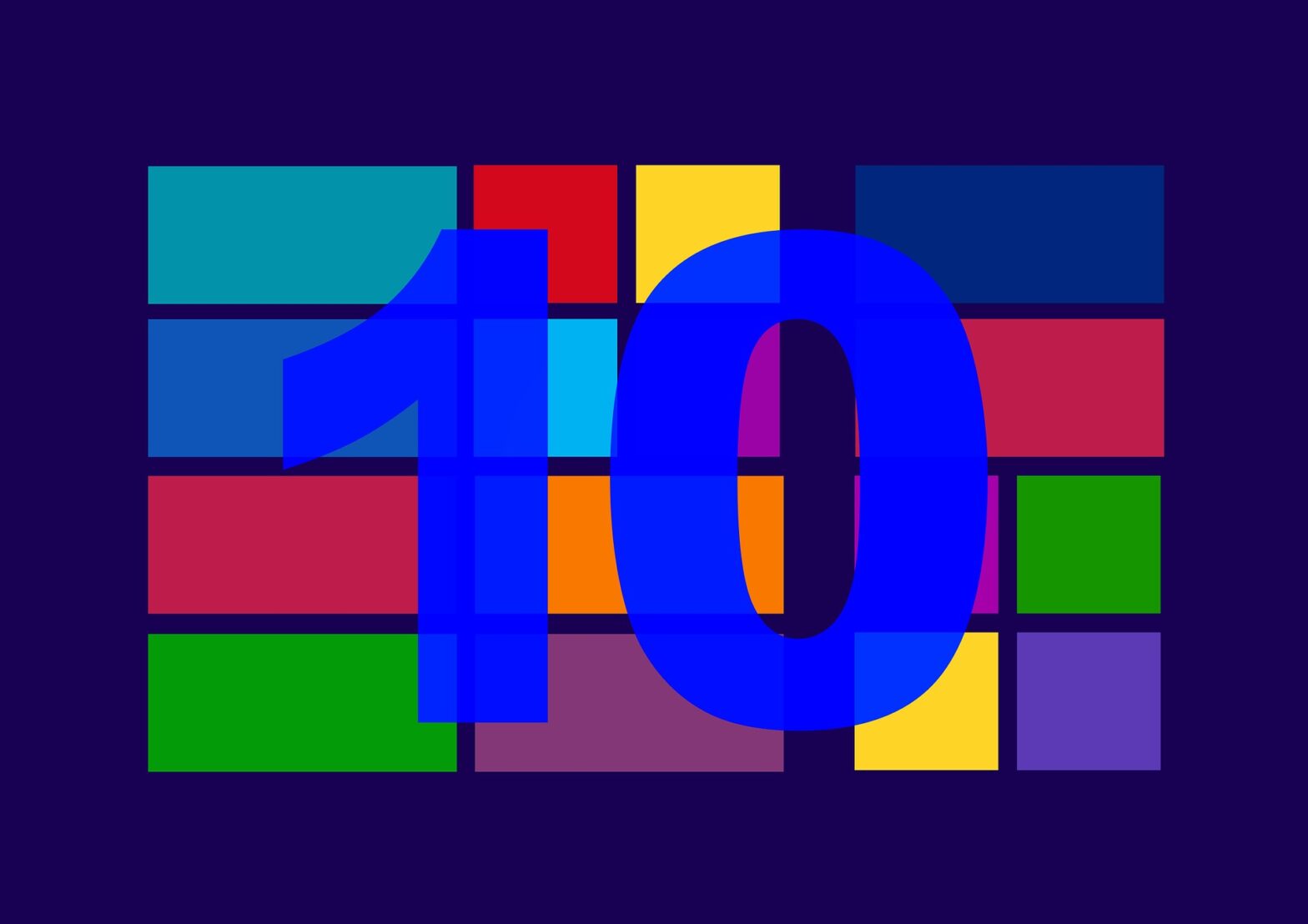
What you need to know about Windows end of life support in 2025
Reading Time: 2 minutes As part of Microsoft’s Modern Lifecycle Policy, the Company is ending all active support for Windows 10 on October 14th, 2025.
High-speed Internet, available almost anywhere on Earth
Reading Time: 2 minutes ‘Connectivity where you least expect it’. That’s a bold statement to make, but can the world’s most advanced internet system, do exactly what it says it can do?
UK water company confirms cyber attack
Reading Time: 3 minutes Southern Water confirms network breach, as cybercriminals Black Basta attempt to hold the UK utility to ransom as they threaten to release data.
The ultimate guide to protecting your company from cyber threats
Reading Time: 3 minutes You go into your office and find yourself locked out of your computer and, it gets worse you’re being asked for a ransom to retrieve your access, here’s how you can stop that.
CNC integrates with FluidOne, aligning with a group of premium brands
Reading Time: 3 minutes CNC provides the very best in IT services, expertly delivered across the Southeast. But now, customers will also benefit from a wider product portfolio supported by FluidOne, a nationwide, market-leading provider of Connected Cloud solutions.
Protecting your data: Lush’s response to its recent cyber attack
Reading Time: 2 minutes Lush the cosmetics store, home to some of the most beautiful fragrances in the high street, has announced on its website, that it had been the victim of a cyber security incident.
Outsourced IT Support: Finding the Perfect Fit for Your Company
Reading Time: 4 minutes Outsourced IT support is just like a marriage. It’s about finding an IT partner who is going to go through all the joys and wonders of business life, with your hand in hand.
Preparing for Cyber Essentials
Reading Time: 4 minutes This guide is intended to set out the process of preparation and gaining the Cyber Essentials and/or Essentials Plus certification.
SonicWall SSLVPN – Standard
Reading Time: 5 minutes A VPN allows you to access resources on your office network from wherever you are. SonicWall NetExtender is a piece of software that can be installed on your laptop or desktop that initiates the VPN connection.
40 Governments around the world crack down on paying out to ransomware gangs
Reading Time: 4 minutes Ransomware attacks are the number one tool used by cyber criminals to steal money and data, which creates havoc upon the social apparatus of society.
Microsoft 365 Copilot – A Vision of Things to Come
Reading Time: 4 minutes We spend an average of about 37 hours a week at work, of which 68% is spent on ‘doing stuff,’ spending time on various tasks, creating more tasks and attending meetings. Don’t we just love those meetings?
Common Mistakes to Avoid in Backup and Disaster Recovery
Reading Time: 4 minutes In today’s data-driven world, backup and disaster recovery have become crucial aspects of any business’s IT infrastructure.
10th October 2023 (Windows 2012)
Reading Time: 5 minutes You would be absolutely right in thinking that the date 10th October, is only 10 weeks away from Christmas. However, the 10th of October 2023, is a very special day in its own right. It is in fact, the last day of support and security from Microsoft for Windows Server 2012, and Windows Server 2012/R2.
Exploring the Benefits of Microsoft 365 for Businesses
Reading Time: 5 minutes In today’s fast-paced and interconnected world, businesses are continually seeking ways to enhance productivity, streamline operations, and stay competitive.
Outsourced IT Support, Is it really worth it?
Reading Time: 6 minutes In today’s rapidly evolving business landscape, you’d be hard-pressed to find a business or sector that doesn’t rely on IT in one form or another.
The Crucial Role of a Chief Information Security Officer (CISO)
Reading Time: 5 minutes In today’s digital landscape, businesses face an ever-increasing threat of cyber-attacks and cybercrime. As organisations become more reliant on technology and data, the need for advanced security measures to protect against cyber threats has become paramount.
The Essential Components of a Reliable Backup and Disaster Recovery Strategy
Reading Time: 4 minutes Businesses today heavily rely on their data and IT infrastructure to operate smoothly and efficiently.
Lend Me Your Ear
Reading Time: 4 minutes The vast array of headset models can make choosing a suitable one somewhat daunting. In this short article I aim to help you identify a headset suitable for your needs.
The Benefits of Outsourced IT Support for Small and Medium-Sized Businesses
Reading Time: 4 minutes In today’s digital age, technology plays a crucial role in the success of small and medium-sized businesses (SMBs). However, managing and maintaining an efficient and secure IT infrastructure can be a daunting task for many SMBs.
Reviewing 365 Phishing Reports
Reading Time: 4 minutes In this guide, it will cover how to view the 365 Phishing reports as well how to check who has completed training if they have been caught out by a Phishing simulation.
Mailbox Housekeeping
Reading Time: 5 minutes In an age where so much communication is electronic it’s easy to forget that your mailbox does have a finite size. Like a filing cabinet there is only so much you can store in it before it becomes full and you have to fillet out old documents to make way for newer ones.
MOVEit File CyberHack
Reading Time: 4 minutes Cybercriminals known as Cl0p ransomware group, thought to be part of a Russian crime ring, have exploited a newly discovered flaw within the popular MOVEit file transfer software.
Microsoft 365 Email Encryption
Reading Time: 3 minutes Although many people don’t realise it, an email is not a secure communication medium by default. Think of it like writing on a postcard and then posting it. Along it’s journey to the recipient anyone can read the contents.
Protecting Your Business from Cybersecurity Threats: Top Tips for Enhanced Security
Reading Time: 4 minutes Cybersecurity is not just about technology; it’s about people, processes, and awareness.” – Vishal Salvi In today’s digitally-driven world, businesses face an ever-growing threat landscape when it comes to cybersecurity. Cybercriminals are continuously devising new techniques to exploit vulnerabilities and compromise sensitive data. As a result, safeguarding your business from cyber threats has become more… Continue reading Protecting Your Business from Cybersecurity Threats: Top Tips for Enhanced Security
Antivirus vs EDR what’s the difference?
Reading Time: 5 minutes When the picture above was taken sometime in the early 80’s, Anti-Virus (AV) protection was almost unheard of. The idea that someone would create a malicious program that would cause your computer to fail was in its infancy.
How to setup a Microsoft 365 App Password
Reading Time: 4 minutes Some applications do not support Multi-factor authentication which can become a problem when Security defaults or Conditional Access have been enabled on a Microsoft 365 tenant. To overcome this we can create App Passwords that can be used to connect to Microsoft 365 Services for a specific application.
Mobile Device Enrolment – iPhone
Reading Time: 6 minutes This useful guide will take you through the steps of enrolling your iPhone with Microsoft’s Mobile Device Management so you really can keep your personal and work data separate.
Mobile Device Enrolment – Android
Reading Time: 6 minutes It’s quite normal to want to have access to email & your calendar on the move but what security considerations need to be taken into account to keep your personal data and company data separate?
Microsoft 365 MFA Setup Guide
Reading Time: 5 minutes Multi Factor Authentication (MFA) provides an additional level of security to your systems and helps combat cyber attacks. When you login to a service such as Remote Desktop Server or Microsoft 365 not only do you enter your username and password but also via the MFA app prompt you confirm it’s you
Protect your business with Cyber Essentials.
Reading Time: 5 minutes Today in the digital age, we store information electronically. Why? Because information is power; it can be our competitive advantage over other businesses. Our supplier list of who provides us with what, and when; it might be customer information, entrusted to us through a sales transaction and numerous other details, all particular to our business.
What is Patch Management?
Reading Time: 4 minutes Whatever your favourite canine might tell you, “Get off the sofa, stop chasing cars, begging for food, digging up the garden, or chewing the furniture”, whether your dog is called Patch or not, you’d be right in thinking, patch management is none of the above.
Mailbox Management
Reading Time: 5 minutes Email has given us a powerful medium to communicate across continents, or just to the other side of the room. With it comes a high volume of messages, many of which are “cakes in the kitchen” style and others that contain large attachments.